SCADA Basics
SCADA Security on Cloud – Securing ATSCADA Cloud Systems
Cloud SCADA, also known as IoT/IIoT-based SCADA, represents a natural evolution of traditional SCADA systems in the era of Industry 4.0 and the IoT Systems ,a concept widely discussed in SCADA BASIC. By leveraging cloud technology, Cloud SCADA enables seamless remote access, monitoring, control, and reporting anytime and anywhere, significantly improving operational flexibility.
In addition, Cloud SCADA allows multiple distributed plants to be connected and unified into a centralized system, while enabling multiple clients to simultaneously participate in system operations. This enhances collaboration and scalability across industrial environments.
However, alongside these advantages come critical challenges. Among them, SCADA Security is one of the most important concerns. Risks related to cybersecurity threats, unauthorized access, and potential system attacks must be carefully considered to ensure safe and reliable industrial operations.
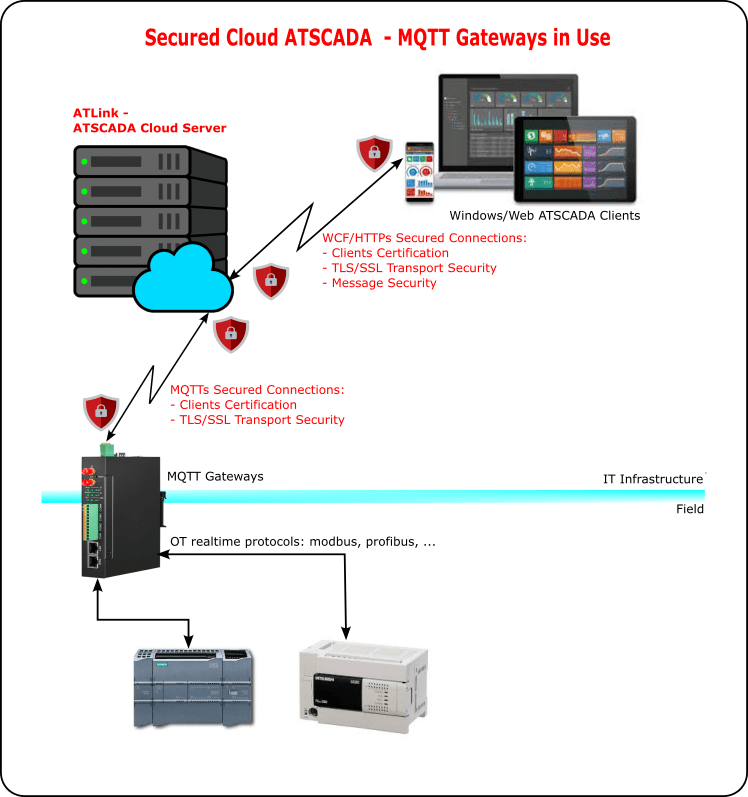
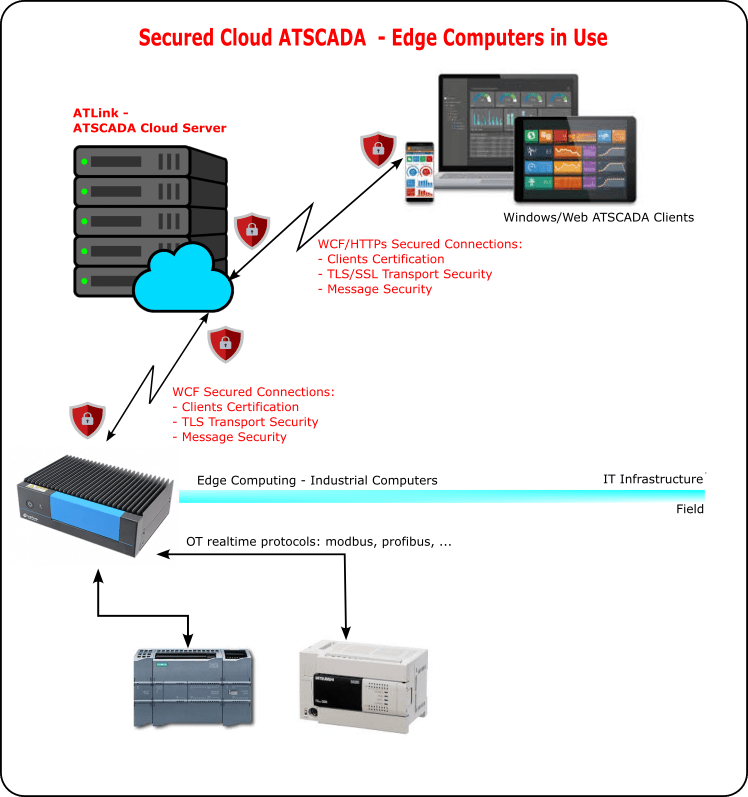
A distributed Cloud SCADA system typically consists of four main components: the cloud server, remote clients operating on IT infrastructure, field-level devices, and a cloud gateway, forming a typical SCADA software architecture. This architecture plays a critical role in enhancing SCADA Security while ensuring scalability and real-time data processing.
The cloud server acts as the central core of the system and is deployed in a public or private WAN environment. It is responsible for handling large volumes of bidirectional real-time data and supporting data acquisition and storage in databases.
In the ATSCADA Cloud system, ATLink acts as the cloud server and serves as the central hub for data processing, communication, and system management, playing a critical role in the overall SCADA security framework.
The cloud gateway transmits real-time data to remote supervisory clients, where users can monitor it through web interfaces or WinForms applications.
The cloud server receives control commands and configuration signals from remote clients and sends them back to the cloud gateway, which then executes the commands or updates information for field-level devices.
These field devices typically include PLCs , HMIs, smart energy meters, smart water meters, and other industrial equipment. This bidirectional data flow is essential for maintaining efficient operations and strengthening SCADA Security in distributed systems.
On the market, there are generally two main types of cloud gateways used in Cloud SCADA architectures:
MQTT Gateway in SCADA Security Systems
The first type is the MQTT gateway, which acts as a data bridge between the field layer and the IT layer using the MQTT protocol. It is widely used for lightweight, efficient data transmission and plays an important role in maintaining stable communication within SCADA Security environments.
Edge Computing Gateway in SCADA Security Systems
The second type is the edge computer, which performs a similar role to an MQTT gateway but with additional capabilities. Edge computers can process a significant portion of data locally, enabling faster response times for monitoring and control of directly connected field devices.
Compared to MQTT gateways, edge computers handle more complex real-time bidirectional data processing. They are typically industrial-grade mini computers equipped with powerful Intel processors, whereas MQTT gateways often use ARM-based chips. This makes edge computing a more robust solution for advanced SCADA Security and high-performance industrial applications.
Engineers deploy MQTT gateways and edge computers across multiple locations in many Cloud SCADA projects to support distributed system architectures. This approach allows systems to handle both simple and complex data processing tasks locally, optimizing performance while maintaining strong SCADA Security, similar to many SCADA applications in industry
By combining these two technologies, businesses can achieve a cost-effective architecture that balances real-time processing needs and system scalability. This distributed model not only improves operational efficiency but also enhances the overall reliability and security of the SCADA Security framework.
Attackers target Cloud SCADA systems to disrupt IT infrastructure, steal production data, or gain control of field devices, posing serious risks to critical sectors such as power plants, transportation systems, and water management. Ensuring strong SCADA security is essential to prevent these threats.
- At the factory (field) level, internal personnel or OT integrators may exploit system access during operation or maintenance to extract data or issue unauthorized commands to PLCs, HMIs, and other devices.
- At the IT infrastructure level, complex software systems, communication networks, and large databases—especially over public WAN—create higher exposure to large-scale cyberattacks.
Common threats include DoS, MITM, APT/zero-day, and SQL Injection attacks, all of which can severely disrupt operations and compromise overall SCADA system security if not properly mitigated.
DOS Attacks
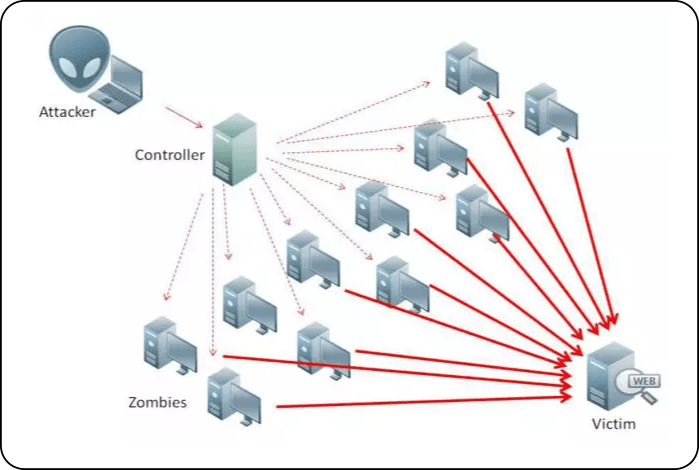
Attackers launch DoS (Denial-of-Service) attacks to disrupt systems or block connectivity, preventing users from accessing services. They overwhelm the target with excessive requests until it can no longer respond, effectively denying service to legitimate users. Typically, a single machine carries out a DoS attack.
In Cloud SCADA environments, DoS attacks often target the cloud server. While they do not typically aim to steal sensitive data, they can severely disrupt real-time bidirectional data flow for monitoring and control. This leads to system congestion, interruptions, and reduced performance, posing a significant threat to SCADA Security.
MITM Attacks
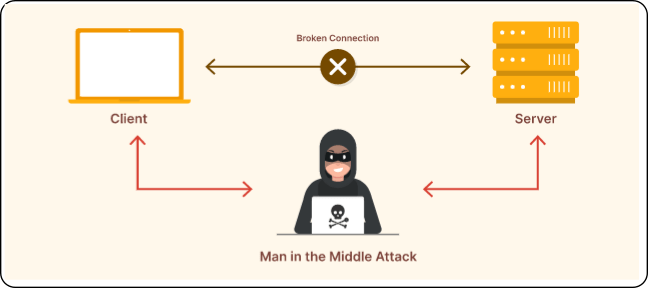
MITM (Man-in-the-Middle) Attacks: A MITM attack is a type of cyberattack in which the attacker gains control over communication connections by exploiting vulnerabilities in communication protocols or by decrypting/encrypting traffic to insert themselves between two communicating parties. This type of attack is stealthy and difficult to detect, making it a serious concern for SCADA Security.
In Cloud SCADA systems, MITM attacks can occur at communication points such as between the cloud gateway and the cloud server, or between remote clients and the cloud server. The goal of a MITM attack is to intercept and collect real-time data or inject false signals into the system. Attackers can use these fake commands to control field devices, posing a critical threat to system safety and overall SCADA security.
APTs or Zero Day Attacks
APTs or Zero-Day Attacks: These attacks exploit vulnerabilities in daily operations, such as email usage, web browsing, or entertainment activities on client machines. Attackers take advantage of security flaws in client software or web applications to deploy malware, viruses, spyware, or backdoors. This type of attack is considered highly dangerous in the context of SCADA Security.
Once attackers gain access to remote clients or the cloud server, they can extract sensitive data, monitor system activities, and even take control of field devices. This poses a severe risk to system integrity, operational safety, and overall SCADA Security in Cloud SCADA environments.
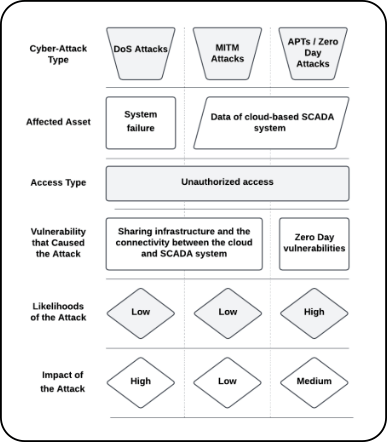
Figure 5 presents a comparison table of key SCADA Security aspects, including the impact of the attack, likelihood of occurrence, vulnerabilities that may lead to attacks, access type, and affected assets.
SQL Injection Attacks
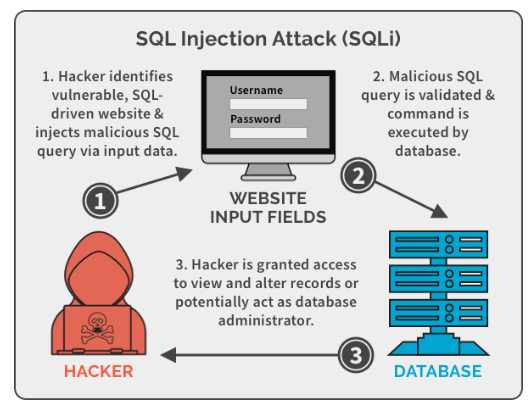
SQL Injection Attacks: SQL Injection is a technique that exploits vulnerabilities in application queries by inserting malicious SQL code to alter the original query. This allows attackers to access and extract data from the database. In the context of SCADA Security, this type of attack is particularly dangerous.
Attackers use SQL Injection in Cloud SCADA systems to extract sensitive data such as production recipes and historical SCADA records. Weakly encrypted credentials can enable advanced attacks like APT or zero-day exploits, potentially leading to full control over system monitoring and operations.
SCADA Security Solutions for ATSCADA Cloud Systems
Hardware & Infrastructure Security
ATSCADA secures Cloud SCADA systems with multi-layer protection across factory and IT environments. At the field level, engineers protect PLC and HMI firmware using access control and authenticated logins, allowing only authorized personnel to operate and maintain the system.
At the infrastructure level, the ATLink cloud server runs on high-performance systems with integrated firewalls in international-standard data centers such as Viettel IDC, enabling traffic monitoring, IP tracking, and blocking of suspicious connections. Engineers also deploy IDS/IPS, restrict access to trusted IPs, enforce updates and endpoint protection, and prioritize local control over cloud-based control to reduce risks from DoS/DDoS, APT, MITM, zero-day, and SQL Injection attacks. Regular cybersecurity training further minimizes human-related risks.
Communication & Data Security
ATSCADA strengthens communication security to prevent MITM and data interception. MQTT systems use MQTT over TLS (MQTTs) with authentication and encrypted data transmission.
ATSCADA communicates with ATLink via WCF, applying authentication and both message-level and TLS encryption, while ATLink secures connections with remote clients using WCF, client certificates, and HTTPS SSL. These measures ensure end-to-end protection and reinforce overall SCADA security.
Conclusion
ATSCADA Lab applies comprehensive solutions to ensure the safety of Cloud ATSCADA systems during deployment, minimizing security risks across both IT infrastructure and OT systems while strengthening overall SCADA security.
While we continuously strive to deliver the best possible solutions, we recognize that there is always room for improvement. ATSCADA Lab continuously enhances its security solutions to better protect Cloud SCADA systems over time.
We also highly value the collaboration of our customers in training operational personnel. Together, we can ensure a higher level of safety and reliability for the entire Cloud SCADA system and maintain strong SCADA Security.
ATSCADA - Providing ATSCADA software - The monitoring and data acquisition control system is the appropriate choice for integrated system projects, IoT, smart city projects, agriculture 4.0... Is trusted by many customers.

Related posts
SCADA and IoT : Modern Industry 4.0
Industry 4.0 is creating a major transformation in the way businesses operate and manufacture. The [...]
Apr
ALL ABOUT SCADA SYSTEM
The SCADA system is the combination of hardware devices and software that allows monitoring and [...]
Oct
SCADA – IoT: Công Nghệ Bổ Sung Cho Công Nghiệp 4.0 Hiện Đại
Công nghiệp 4.0 đang tạo ra sự thay đổi lớn trong cách các doanh nghiệp [...]
Sep
Xu hướng ứng dụng hệ thống scada trong công nghiệp
Các hoạt động sản xuất công nghiệp ngày nay càng cao đòi hỏi nhiều tiêu [...]
Dec
Everything You Need to Know About SCADA Systems
A SCADA Systems is a combination of hardware devices and software that enables remote monitoring [...]
Dec
SCADA System Software Architecture Overview
The SCADA System Software architecture is a combination of two main parts: execution software (runtime [...]
Jan